We are often asked how we are able to calculate metrics as described here:
And demonstrated/explained here:
In this installment I will explain how you can calculate Return on Investment of any security tool using reclaimed FTE labor hours as the purchase justification.
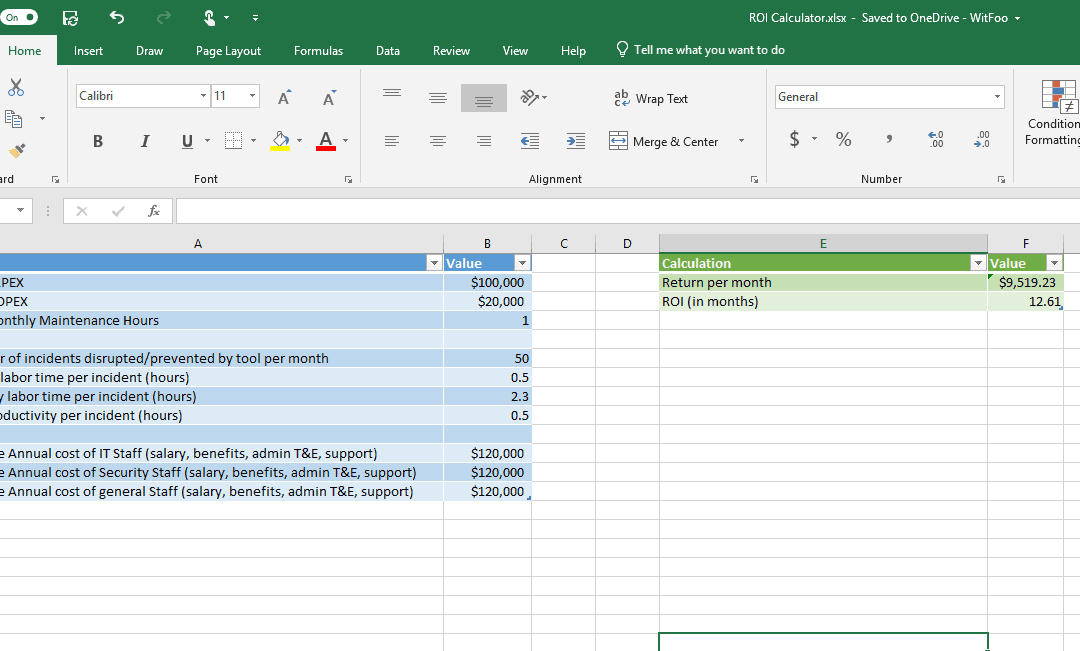
tldr; – Just Download the Spreadsheet
I put together an Excel spreadsheet that does all the calculations I am going to explain below. If you don’t need to know how the sausage is made, feel free to download it and plug in your numbers.Download here: ROI Calculator.xlsx
The calculations explained
The first variable is work cycle count in a period represented as n. n is the number of incidents stopped/disrupted by the tool in a period (usually a month.)
Labor cost c is calculated by dividing the yearly cost of an FTE by work hours (40 hours per week, 52 weeks = 2,080). A low annual FTE costs that reflects salary, benefits, T&E & equipment & service costs is $120,000. Divided by the 2,080 gives an hourly labor cost of $57.69. Note most enterprise organizations have labor costs that are 2 to 3 times this cost.
The median cycle time to fix an incident is the number of labor hours required in each cycle (n) to detect, contain, repair & report on the cycle and is represented by t. Cycle times vary based on incident type, process, policy & tools. In the case of phishing, minimum process requires a password reset of the effected credential and blocking of the phish url. Diligent organizations will also need to review network & system logs to determine impact and may choose to monitor dark web for disclosures. Organizational ticketing & reporting systems add to cycle time as well.
To calculate ROI you need to calculate return rate: r = n*t*c. Keep in mind that n is calculated against a period. We tend to recommend a month as the period. r will give you the return in dollars each period from implementing the tool. ROI = cost of tool / r. The unit will be the period of n and r (recommended as months.) There are 3 types of costs associated with the tool 1) capital expenditure 2) operational expenditure and 3) labor cost to keep it running. Overlooking labor cost is a common ROI mistake that can skew calculations against the interests of the purchasing customer.
Also note that this is “hardest ROI.” It only addresses the most concrete return numbers: IT Labor cost reduction. A secondary cost is loss of productivity which can be calculated by updating t to reflect time the end user (that was phished) cannot work during remediation. In phishing, this is generally an additional 15 to 90 minutes per cycle. The “soft cost” is the loss of proprietary data or brand erosion. We are researching models for calculating this but key data is not available currently which makes the math unreliable (soft.) For that reason we don’t use it in ROI calculations in spite of the expectation that it has a much larger cost impact. Businesses work off of math that can be defended not FUD or “modeled projections.”
Summary
Return on Investment (ROI) calculations are the most effective mechanism for explaining security tool investments to the organizational executives. Spend x to reduce costs by 2x is very easy for business executives to support. The devil is in the details, however. The pre-purchase ROI projection needs to be met or exceeded after purchase if the next visit to the well is going to be effective. That can be simply accomplished by avoiding soft/fuzzy math and sticking to concrete returns that are easy to explain, calculate and test.