The following abstracts are available for delivery at security meetings and conferences.
Bio
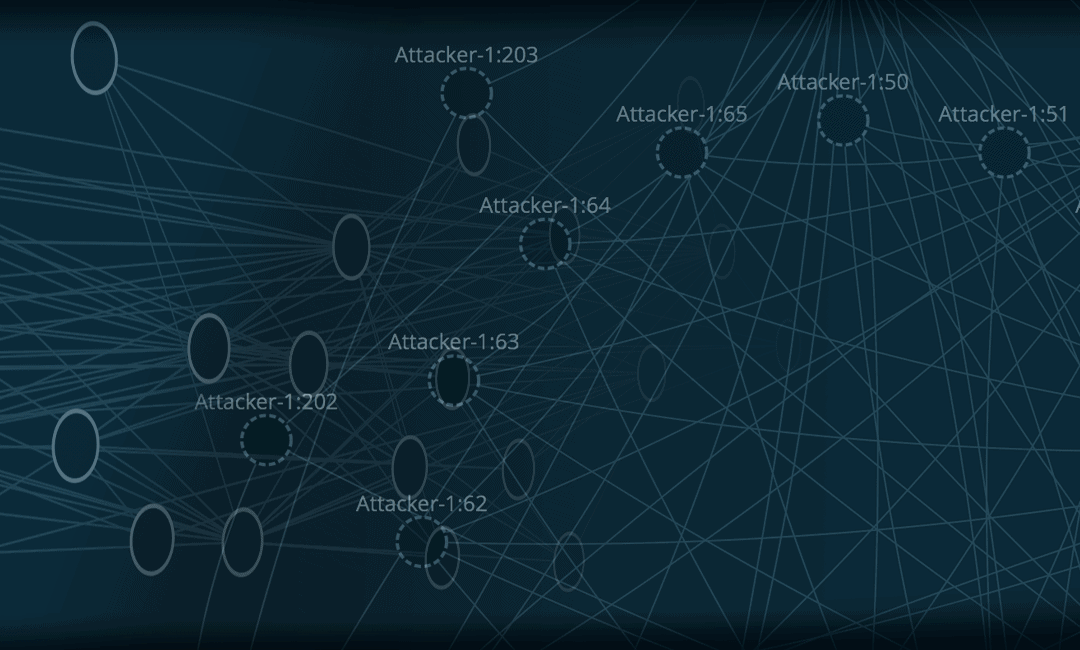
Charles Herring is co-Founder and Chief Technology Officer at WitFoo. WitFoo was founded to enable the sharing of information and operations across the craft of Cybersecurity. Charles leads research and development of the WitFoo Precinct platform that utilizes Apache Cassandra as a fundamental component in its architecture. Precinct ingests trillions of messages each day across hundreds of clusters to detect cybercrime and provide secure methods of sharing data and operations across corporations, organizations, law enforcement, national security and insurers.
Charles regularly speaks on research at conferences including DEFCON, Secure360 and GrrCON. Charles began his career in cybersecurity analytics in 2002 while in the US Navy serving as the Network Security Officer for the Naval Postgraduate School. After leaving active duty in 2005, he ran a consulting company that focused on data and operations sharing across private and public sector organizations. In 2012, Charles joined network behavioral and anomaly company, Lancope designing and deploying advanced network security solutions. In 2015, Charles joined Cisco Systems through the Lancope acquisition and supported the Global Security Sales Organization until launching WitFoo in 2016.
When Charles is not researching challenges in big-data and cybersecurity, he enjoys SCUBA diving, travel and long dinners with his wife, Mai.
Building a Global CyberGrid on Cassandra
Technical Level: Intermediate to Advanced
Audience: Data Engineers/Scientists/Developers
Detecting, catching and successfully prosecuting cybercrime requires collaboration across private sector, law enforcement, insurance companies and national security agencies. Even small organizations produce gigabytes to terabytes of evidence across their internal and cloud instances. Much of this signal evidence contains information protected by law.
Law enforcement needs to collect evidence from victim organizations without spending hundreds of labor hours. Organizations need a manner to package and share evidence with law enforcement without creating undo risk. Insurers need effective ways of underwriting policies and adjusting claims associated with cybercrime.
In this session, Charles Herring, co-founder and Chief Technology Officer of WitFoo, will detail how terabytes of data collected across hundreds of independent Cassandra clusters each day or safely leveraged to meet the goals of reducing cybercrime and its associated costs.
Charles will cover, build Cassandra schemas to enable cross-organizational sharing, using REST API for facilitating transport across clusters, leaning into Cassandra TTL for data garbage collection and best practices to ensure resilience and performance in diverse environments.
SECOPS Driving Criminal Prosecution
Technical Level: Beginner & Intermediate
Audience: Security Managers/Executives, Incident Responders
At a key point in the history of cybersecurity operations, it was passively decided that SECOPS is an extension of IT OPS. This session will examine the thesis that SECOPS is an extension of the craft of Law Enforcement and the consequences of building SECOPS on IT models (that were derived from manufacturing models.) Approaches from Law Enforcement that can accelerate and improve SECOPS will be examined. Methods of safely leveraging law enforcement to reduce cyber risk and costs will also be demonstrated.
Resources: https://www.witfoo.com/infosec-craft/secops-driving-prosecution/
FLIGHT DECK INFORMATION ASSURANCE AUDITING
Technical Level: Beginner
Audience: Security Managers/Executives, Auditors
Naval Air Training and Operating Procedures Standardization (NATOPS) is said to be “written in blood.” NATOPS was created in 1961 after nearly 50 years of the US Navy flying aircraft. The extensive system was created to stop the extreme failures that resulted in the loss of hundreds of lives and billions of dollars in loss.
Between 2015 and 2017, WitFoo researchers worked with organizations from higher education, Fortune 500, healthcare and mid-market to test NATOPS quality assurance (QA) approaches in cyber security and information security auditing.
In this session, the following experiments and findings will be discussed:
- Defining the correct “unit of work” in security operations (borrowing from Maintenance Action Forms.)
- “Data Evolution” of extremely technical information that can be understood by executives (and Admirals).
- Ongoing, organic metric collection and analysis in contrast with inspections and audits
- Separating human audits and architecture audits
- Improving auditing using NATOPS Readiness Inspections approaches
The session will include data and demonstrations of the findings.
CRUISING ON A SECURITY DATA LAKE: SOLVING BIG DATA CHALLENGES IN SECOPS
Technical Level: Advanced
Audience: Data & System Architects, Developers
Researchers at WitFoo in conjunction with The University of Chicago and representatives from Law Enforcement, US Military and Fortune 500 organizations conducted more than 2000 controlled experiments on production networks from 2016 through 2018 to establish a Big Data pipeline for use in CyberSecurity Operations that allows for the application of investigative workflows and indicators of compromise in near realtime as well as providing for retrospective analysis of the complete data stack when new insights and indicators are made available. The first section of the session will evaluate the strengths and limitations of Big Data technologies including Elasticsearch, Splunk, Hadoop, Kafka, MySQL NDB, Cassandra, NoSQL vs RDBM as well as pipeline philosophies including streaming and batch processing. The second section will outline the specific approaches that are used in the discovered pipeline. Detailed demo and code will be provided to illustrate adaptive and retrospective parsing, event generation and data evolution. The third section will provide a demonstration of the pipeline in use to detect emerging threats and to retrospectively find threats missed historically. Upon completion of the session, attendees will understand the philosophies, components and steps in creating an effective big data pipeline that addresses the challenges in Cyber Security Operations.
BREAKING NBAD AND UEBA DETECTION
Technical Level: Intermediate
Audience: Incident Responders, Penetration Testers
Network Behavior Anomaly Detection (NBAD) and User and Entity Behavior Analytics (UEBA) are heralded as machine learning fueled messiahs for finding advanced attacks. The data collection and processing methodologies of these approaches create a series of new exploitable vectors that can allow attackers to navigate network and systems undetected. In this session, methods for poisoning data, transforming calculations and preventing alerts will be examined. Proof of concept Python code will be demonstrated and made available. Approaches to harden against these attacks will also be discussed as well as outlining needed changes in detection standards.
Resources: https://www.witfoo.com/infosec-craft/breaking-nbad-ueba-deck/
METRIC DRIVEN DEVOPS
Technical Level: Advanced
Audience: Data & System Architects, Developers
Developing software that changes the world, exceeds customer expectations, provides turn-key functionality in diverse scenarios while meeting security and compliance requirements is the holy grail of Security Development Operations (SECDEVOPS). There are thousands of variables that need to be constantly addressed to find the balance that delivers sustainable and secure success. In this session, WitFoo’s chief engineers will outline an innovative approach to secure devops called Metric Driven Development. It will cover the following topics:
- Creating a metric collection infrastructure to alert on security and functionality deficiencies
- Utilizing metrics to write optimized unit and system tests
- The optimal value of code coverage, application pen-testing and static code analysis
- Integrating metrics into customer support evolutions
- The place of containerization in SECDEVOPS
- Build metric driven use cases from hypothesis to pivot
By the conclusion of the session, attendees will have the tools necessary to implement lean and effective development pipelines that deliver secure and useful code in a fraction of the time and at a fraction of the development cost.
Key learning points:
- Creating a metric collection infrastructure to alert on security and functionality deficiencies
- Utilizing metrics to write optimized unit and system tests
- The optimal value of code coverage, application pen-testing and static code analysis
Resources: https://www.witfoo.com/infosec-craft/exploit-con-slides-metric-driven-secdevops/
FEDERATING CYBERSECURITY OPERATIONS
Technical Level: Beginner
Audience: System Architects, Security Managers, Incident Responders, Underwriters, Auditors
Cybersecurity operations (SECOPS) requires a team possessing a wide range of skills including security frameworks, a long list of security technologies, legal, criminal investigation, forensics and risk management. Most organizations are not able to staff personnel with all those skills at the staffing levels required to address the SECOPS needs of the organization.
Attempts at outsourcing SECOPS to MSSP or other approaches struggle due to factors including risk management, availability of organizational context and diverse security control configurations. Further complicating the sharing of information are the volumes of data processed and regulatory restrictions.
From 2016 to 2020, researchers at WitFoo worked with stakeholders at managed security service providers (MSSP), law enforcement, military, higher education, enterprise and insurance underwriters to develop a SECOPS framework to solve these issues.
In this session, the following topics will be covered:
- Forensically collecting incident data
- Creating a standardized unit of work
- Securely synchronizing data
- Shipping sanitized data to protect risk concerns
- Securely executing SOAR playbooks & data searches remotely
- Sharing workloads between consolidated SOC’s and remote SOC’s
The following use-cases will be examined:
- MSSP operations over many tenants
- Ships at sea federating SOC responsibilities to a Shore SOC
- Reporting health metrics for cybersecurity insurance underwriting
- Creating affidavits for submission to Law Enforcement
- Easing risk during M&A processes
OBJECT ORIENTED SOAR
Technical Level: Intermediate
Audience: Security Managers, Incident Responders, Security Architects
Security Orchestration Automation and Response (SOAR) is a set of features with the intent of reducing security workloads in security operation centers (SOC.) The prevalent approach to SOAR is using low-level playbooks that follow programmatic flowcharts to automatically execute manual workflows when specific message signals or conditions are achieved.
As enterprises have implemented low-level SOAR to create savings, several new challenges have been identified including an unmanageable number of playbooks, unauthorized bypass of institutional change controls, growing staffing requirements and introducing new attack vectors for criminals to exploit.
This session will review research applying approaches from Object Oriented Programing and Big Data pipeline advances to solve the existing SOAR issues while still delivering on the value proposition of SOAR.
The following topics will be covered in the session:
- Finding the appropriate trigger for SOAR
- SOAR as part of change controls
- Different input objects in SOAR
- Contextualizing SOAR to attack types and business considerations
- Reducing SOAR Playbook maintenance costs through abstraction and normalization
THE SEVEN UNSTABLE CONVERSATIONS OF CYBERSECURITY
Technical Level: Beginner
Audience: Any Business or Security Personnel
WitFoo was founded in 2016 to develop the tools and data required to mature the craft of cybersecurity operations. The research at WitFoo has focused on seven unstable conversations within each part of the craft. This session will share the findings on each of the 7 conversations and will explore remedies and impacts of them.
- Investigators do not understand what their tools are saying
- Managers cannot track security practice success
- Security practice cannot express value to business
- Security vendors cannot be held accountable
- Organizations cannot safely share information with each other
- Organizations cannot safely report crimes to law enforcement
- Law enforcement lacks evidence to prosecute criminals
MACHINE LEARNING IN PSYOPS & SOCIAL ENGINEERING
Technical Level: Intermediate
Audience: Any Business or Security Personnel
Machine learning (ML) is arguably the most potent advancement in technology since atomic fission with similar benefit and risk extremes. The outcome driven nature of machine learning allows computers to rapidly test theories to find pathways to support specific goals. These approaches applied to social engineering can be used to manipulate human factors for purposes including cybersecurity breach. This session will cover the philosophies, strategies and tactics used to accomplish a successful campaign to recruit human assets to a cause. Factors to mitigate risk in these advanced social engineering attacks will also be examined.